20 Insecure Port Details and Their Secure Alternatives
Introduction
In the realm of network security, understanding port numbers and their vulnerabilities is crucial. This article delves into 20 Insecure Port Descriptions and Their Secure Alternatives, shedding light on their risks and offering secure alternatives to fortify your network.
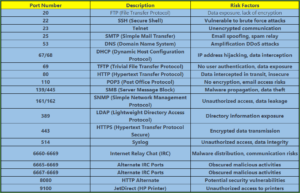
Insecure Port Details | Descriptions
Below, we present a comprehensive list of insecure port descriptions, along with the potential risks they pose to your network:
Secure Alternatives
Now, let’s explore secure alternatives to these insecure ports, enhancing your network’s security:
- SSH (Secure Shell) – Port 22: Secure your remote access with SSH, which uses encryption and secure authentication methods.
- HTTPS (Hypertext Transfer Protocol Secure) – Port 443: For secure web browsing, use HTTPS to encrypt data transmitted between your browser and the website.
- SMTPS (Secure SMTP) – Port 465: Use SMTPS for encrypted email communication, reducing the risk of email spoofing and interception.
- SFTP (SSH File Transfer Protocol) – Port 22: When transferring files securely, opt for SFTP over FTP for data encryption.
- DNSCrypt – Port 443: Protect your DNS queries with DNSCrypt to prevent DDoS attacks and data exposure.
- HTTP over TLS/SSL – Port 443: Ensure web application security by using TLS/SSL to encrypt data on Port 443.
- LDAPS (LDAP Secure) – Port 636: Secure your directory access with LDAPS, encrypting sensitive directory information.
- FTP over TLS/SSL – Port 990: Make your FTP transfers secure by using TLS/SSL encryption on Port 990.
Conclusion
Insecure port descriptions can leave your network vulnerable to various risks. However, by replacing them with secure alternatives, you can significantly enhance your network’s security. Protect your data, devices, and communications by making informed choices regarding port usage.
FAQ
Q1: What is the importance of securing network ports? A1: Securing network ports is essential to protect against unauthorized access, data interception, and various cyber threats. Insecure ports can expose your network to significant risks.
Q2: How can I check if a port on my network is secure? A2: You can use port scanning tools and network security software to assess the security of the ports on your network. Regular security audits are recommended.
Q3: Are there other secure alternatives for the listed insecure ports? A3: Yes, there are often multiple secure alternatives for insecure ports. Research and choose the one that best suits your specific network requirements.
Q4: Is it necessary to change default port numbers for added security? A4: Changing default port numbers can add an extra layer of security, as it makes it more challenging for attackers to identify and exploit vulnerable services.
Q5: Can I change port numbers on my network without causing disruption? A5: Changing port numbers can be done, but it requires careful planning. It’s best done during maintenance windows or off-peak hours to minimize disruption.
Q6: What are some common tools to enhance network security? A6: Utilizing firewalls, intrusion detection systems, and encryption protocols are common methods to enhance network security.
Q7: Is it necessary to invest in professional network security services? A7: The complexity of network security depends on the size and type of network. Smaller networks may benefit from off-the-shelf security solutions, while larger enterprises often require professional services to ensure comprehensive protection.
Q8: What are some best practices for maintaining network security? A8: Regularly update and patch software, implement strong password policies, educate users about security best practices, and conduct security audits to identify vulnerabilities.
conclusion, safeguarding your network against potential vulnerabilities requires a proactive approach. Understanding insecure port descriptions and replacing them with secure alternatives is a fundamental step toward a more secure digital environment. You can significantly reduce the risks associated with network vulnerabilities. Remember, a secure network is not just a necessity; it’s a proactive stance against potential threats in the digital age.
You can also read : Best Network Internet Run Commands for Windows